- If AhnLab cannot assist with the variant you are dealing with, then unfortunately there is no other known method that I am aware of to decrypt files encrypted by Magniber without paying the ransom.
- AhnLab 보안 제품과 서비스 구성을 한. (Magniber) 랜섬웨어, 크립트엑스엑스엑스(CryptXXX) 3.x 버전, 2.x 버전, 나부커(Nabucur), 테슬라크립트(TeslaCrypt)의 일부이며, 신∙변종.
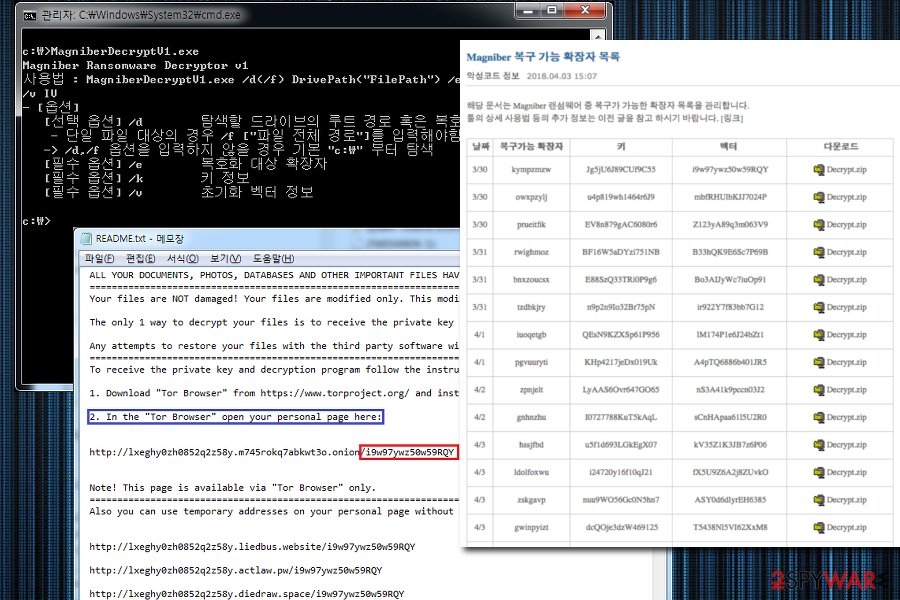
- 그럼 도대체 Ahnlab magniber decrypt 는 왜 사용을 못할까요? 그에 대해 한번 말씀을 드리겠습니다. 안랩에서 매그니베르 복/구툴을 내놓았지만, 4월 이전에 감/염 되셨던 파일들만 진행이 가능하십니다.
Clone via HTTPS Clone with Git or checkout with SVN using the repository's web address. AhnLab Recognized as 2020 South Korea Endpoint Security Vendor of the Year for Two Consecutive Years: 2020-12-17: 327: 227: AhnLab V3 Nominated as Top Product by AV-TEST on October 2020 Evaluation: 2020-12-07: 64: 226: AhnLab Warns of Phishing Website Disguised as Popular Out-of-Stock Items: 2020-11-18: 30: 225.
Magniber is a ransomware distributed by Magnitude's operator. The latest version of Magniber has been upgraded in a comprehensive way in terms of encryption method, infected object, etc. This article comprehensively analyzes the latest version of Magniber from the perspectives of its attack process, harm, behavior analysis, comparison with earlier version, security protection measures, etc. Magnitude EK is a long-lasting browser exploit tool that has been very active since its inception in 2013, and through which multiple ransomware packages have been distributed - from Cerber to Magniber, GangCrab, etc. The tool has been one of the favorite tools for ransomware users worldwide. Magniber is a ransomware distributed by Magnitude's operator. The original version of Magniber mainly targets South Korea and has a relatively simple encryption method. The latest version of Magniber has been upgraded in a comprehensive way, and can infect many Asian countries including China, and has a quite different encryption method. The latest version of Magniber exploits the CVE-2018-8174 VBScript engine memory corruption vulnerability of Internet Explorer (please refer to related article for vulnerability analysis). This article comprehensively analyzes the latest version of Magniber from the perspectives of its attack process, harm, behavior analysis, comparison with earlier version, security protection measures, etc. Magniber's attack process is mainly divided into the following stages: Magnigate's 302 redirection A Base64 obfuscated JavaScript is used to launch Magnitude's landing page A Base64 encoded VBScript is used, the main functionality of which is to determine whether the CVE-2018-8174 vulnerability exists. If the vulnerability exists, the shellcode is executed and the payload (the first dll) is downloaded The dll loader unpacks the Magniber's core dll and injects it into a process Football manager macbook. The core dll completes the proceses of local file traversal and encryption for ransom Let's first take a look at Magniber's traffic view[1], as shown below: (The image is from Malwarebytes [1]) It can be found that after Magnigate's 302 redirection, the Base64 encoded and obfuscated JavaScript and VBScript are called. The original JavaScript is as follows: The decoded JavaScript is as follows: The decoded VBScript main function is as follows (for detailed information about VBScript, please refer to another article 'Microsoft VBScript Engine Remote Code Execution Vulnerability (CVE-2018-8174) Analysis Report'): As can be seen from the VBScript, the functionality implemented by the script is to judge whether the VBScript UAF vulnerability CVE-2018-8174 exists. If the vulnerability exists, the vulnerability is triggered and the type confusion is used to save and execute the constructed Shellcode by constructing the VirtualProtect structure. The shellcode executed is as follows: In terms of functionality, the Shellcode is a simple downloader which will download the obfuscated load dynamic link library (load.dll), decode it with the key through XOR operation, and deploy it. The downloaded load dynamic link library (load.dll) is still not the core of Magniber ransomware. The main functionality of load.dll is to load the next stage program, extract Magniber's core DLL (core.dll), and inject the core DLL into a process. Both DLLs, with Reflective Loader stub, load themselves into a current process using the Reflective DLL injection technique. For the Reflective DLL Injection technique, please refer to [2]. After the core DLL is loaded into the process, it will soon be found that files (including compressed files, Office documents, scripts, images, videos, etc.) in all directories will be encrypted and added with the extension .dyaaghemy, and a README.txt file (roughly means you need to pay a ransom to decrypt the files) will be placed in the current directory, as shown below: The link in the given README.txt points to an onion web interface that is unique to each victim and similar to many other ransomware pages: (The image is from malwarebytes[1]) Each file encrypted by the latest version of Magniber has a .dyaaghemy extension, and each file is encrypted with a unique key. The encrypted content is completely garbled, indicating that a stream cipher or a blockchain cipher (probably AES encryption in CBC mode) is adopted by the attacker. The effect of Magniber infection is as follows (take php file as an example): The latest version of the Magniber contains 2 dlls, of which 72fce87a9766a8c09ed844564adc75 is just the next stage loader that unpacks Magniber's core DLL (19599cad1bbca18ac6473e64710443b7) and injects it into a process. 4.1 Load dll (load.dll) Behavior AnalysisLoad.all code is relatively simple, and its main functionality can be understood through static analysis. The entry function of load.dll is as follows: After getting into the core processing function, we can see that it carries out a process injection, as shown below: Next, open the local notepad and write the data: Query current process information: Get the information about the module loaded by the current process: 4.2 Core dll (core.dll) Behavior Analysis4.2.1 Core.dll Overall Structure4.2.2 Core.dll Specific AnalysisCore.dll Entry: Follow up the execfunc() function. If there is a function pointer in the corresponding position, execute: Follow up the sub_10008768 function to get into the core processing function main(). It first judges the system language, if not Chinese (Hong Kong), Chinese (Macau), Chinese (Simplified), Chinese (Singapore), Chinese (Taiwan), Korean (Korean), Malay (Malaysia), it directly call the function 1000 to exit. Please refer to the link [3] for specific language ID. Then a series of operations on the memory layout are carried out, the result is as follows: Next, the advapi32.dll is loaded to clear the memory area, extend the environment variable string, and replace the environment variable string % PUBLIC% with the current user-defined value: Next, call the 4FA8 function to create the mutex dyaaghemy (the extension of the encrypted files): Call GetTickCount to get 19 random strings: Copy the URL and other information to get the disk drive letter: Get disk information: Encrypt the primary and logical disks: Call 59F7 in 64C4, compare it with the folder under the C drive, and encrypt the disk files: Ahnlab south korea map. Traverse the file, determine whether the file is an executable file and other attribute values, and obtain a random value to prepare for the encryption operation: Use the encryption function provided by the system to generate the encryption key: File encryption: Generate ransom information: Then operate the registry and execute other commands: After all the work is completed, a data pack is sent to report completion: For analysis of earlier version, please refer to link [4]. Compared with the earlier version, the new version mainly has the following changes: (1) A lot of code obfuscation techniques are adopted Compared with previous version of Magniber, a lot of effort has been put into code obfuscation, and the code is obfuscated via a variety of different techniques. First of all, API functions are now dynamically retrieved by their checksums: Dynamic retrieval: a function pointer is obtained by searching the export table of the currently loaded dll. In addition, some of the parameters for the calls are dynamically calculated and junk code is added in between the operations. A string that is supposed to be loaded is scattered through several variables: (2)More countries are targeted The previous version of Magniber only targets South Korea, the new version of Magniber is aimed at more countries. The supported languages are Chinese (Simplified, Taiwan, Singapore), Korean (Korean), Malay (Malaysia), etc. (3) File encryption File encryption of the earlier version depends on the AES key downloaded from the CnC server (if not available, it returns to a hard-coded key, in which case file encryption is relatively easy). This time, Magniber comes with a public RSA key of the attackers that makes it fully independent from the Internet connection during the encryption process. This key is used for protecting the unique AES keys used to encrypt files.
1. The spread of Magniber is mainly based on the Internet Explorer's latest VBScript engine memory corruption vulnerability, namely CVE-2018-8174. Therefore, you first need to fix the vulnerability to avoid the harm of the ransomware. Fix suggestions: fix the vulnerability CVE-2018-8174 according to the vendor-provided patch: https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2018-8174[9]. 2. Deploy an IPS product to block related attacks. HUAWEI has released a signature database to detect CVE-2018-8174, please upgrade to the latest version which can be downloaded at https://isecurity.huawei.com/sec/web/freesignature.do Reference Links [1]https://blog.malwarebytes.com/threat-analysis/2018/07/magniber-ransomware-improves-expands-within-asia/ [2]https://github.com/stephenfewer/ReflectiveDLLInjection [3]https://www.cnblogs.com/wangweixf/archive/2008/08/15/1268537.html [4]https://blog.malwarebytes.com/threat-analysis/2017/10/magniber-ransomware-exclusively-for-south-koreans/ [5]http://wubingdu.cn/download/ReimageRepair [6]http://wubingdu.cn/download/mb3-setup [7]http://asec.ahnlab.com/1124 [8]https://gist.github.com/evilsocket/b89df665e6d52446e3e353fc1cc44711 [9]https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2018-8174 1.Magniber(load.dll): 6e57159209611f2531104449f4bb86a7621fb9fbc2e90add2ecdfbe293aa9dfc 2.Magniber(core.dll): fb6c80ae783c1881487f2376f5cace7532c5eadfc170b39e06e17492652581c2 3.Javascript: https://gist.github.com/malwarezone/62e765a5d238360af68c9ca654cc4513#file-3-vb 4.VBScript: https://gist.github.com/malwarezone/62e765a5d238360af68c9ca654cc4513#file-4-vb |
157****7036 2019-01-29 20:10:44 dsd
My Decryptor ransomware removal instructions
What is My Decryptor?
My Decryptor (also known as Magniber) is a ransomware-type virus discovered by malware security researcher, Michael Gillespie. Once infiltrated, My Decryptor encrypts stored files and appends filenames with an extension comprising seven random characters. For instance, 'sample.jpg' might be renamed to a filename such as 'sample.jpg.gkelhoh'. At this moment cyber criminals are using '.ypkwwmd', '.ndpyhss', '.wmfxdqz', '.axlgsbrms', '.nhsajfee', '.mqpdbn', '.damdzv', '.qmdjtc', '.mftzmxqo', '.demffue', '.dxjay', '.fbuvkngy', '.xhspythxn', '.dlenggrl', '.skvtb', '.vbdrj', '.fprgbk', '.ihsdj', '.mlwzuufcg' or '.kgpvwnr' extensions for encrypted files. After successfully encrypting files, My Decryptor creates a text file ('_HOW_TO_DECRYPT_MY_FILES_[random_characters]_.txt', 'READ_ME_FOR_DECRYPT_[victim's id].txt') or READ_ME.txt, placing it on the desktop.
The text file contains a message stating that files are encrypted and can only be restored using a unique decryption tool together with a unique (private) key. Unfortunately, this information is accurate. It is currently unknown which cryptography My Decryptor ransomware uses, however, as the message mentions a 'private' key, it is safe to assume that the encryption is asymmetric. Therefore, two keys (public [encryption] and private [decryption]) are generated. Cyber criminals store the private key on a remote server. Decryption without this key is impossible. Victims are encouraged to pay a ransom in exchange for the key and decryption tool - they are instructed to visit My Decryptor's website to receive these assets. The cost of decryption is .2 Bitcoin (currently equivalent to ~$1145). It is also stated that the ransom must be paid within five days, after which the cost will double. Be aware that cyber criminals cannot be trusted. Research shows that these people often ignore victims, once payments are submitted. Therefore, paying does not guarantee decryption of your files and there is a high probability that you will be scammed. As well as losing your money, you will support cyber criminals' malicious businesses. Therefore, we strongly advise you to ignore all requests to pay any ransoms. Unfortunately, there are currently no tools capable of restoring files encrypted by My Decryptor. The only solution is to restore your files/system from a backup.
Screenshot of a message encouraging users to pay a ransom to decrypt their compromised data:
My Decryptor shares many similarities with dozens of other ransomware-type viruses. The list of examples includes (but is not limited to) Anubi, BugWare, Asasin, and SyncCrypt. These viruses are developed by different criminals, however, their behavior is identical - all encrypt files and makes ransom demands. The only major differences are size of ransom and type of encryption algorithm used. Research shows that, unfortunately, most of these viruses employ algorithms (foe example, AES, RSA, etc.) that generate unique decryption keys. Therefore, unless the malware contains bugs/flaws or is not fully developed, file decryption manually (without involvement of developers - contacting these people is not recommended) is impossible. For these reasons, ransomware-type viruses such as My Decryptor present a strong case for maintaining regular data backups.
How did ransomware infect my computer?
Ransomware-type viruses are proliferated in various ways, however, the most common are: spam emails, third party software download sources, fake software update tools, and trojans. Spam emails often contain malicious attachments (such as JavaScript files, MS Office documents, etc.) that, once opened, download and install malware. Unofficial software distribution sources (peer-to-peer [P2P] networks, free file hosting websites, freeware download websites, etc.) often present malicious executables as legitimate software, thereby tricking users into downloading and running malware . Fake software updaters exploit outdated software bugs/flaws to infect the system. Trojans are the simplest ones - they merely open 'gates' for other malware to infiltrate the system.
| Name | My Decryptor virus |
| Threat Type | Ransomware, Crypto Virus, Files locker |
| Encrypted Files Extension | 7 random characters. |
| Ransom Demanding Message | _HOW_TO_DECRYPT_MY_FILES_[random_characters]_.txt, READ_ME_FOR_DECRYPT_[victim's id].txt, READ_ME.txt, Tor website |
| Ransom Amount | 0.2 Bitcoin |
| Cyber Criminal Contact | Developers provide support via Tor website. |
| Detection Names | Ad-Aware (Gen:Variant.Razy.518505), BitDefender (Gen:Variant.Razy.518505), Emsisoft (Gen:Variant.Razy.518505 (B)), ESET-NOD32 (A Variant Of Win32/GenKryptik.CUTS), Full List Of Detections (VirusTotal) |
| Symptoms | Cannot open files stored on your computer, previously functional files now have a different extension (for example, my.docx.locked). A ransom demand message is displayed on your desktop. Cyber criminals demand payment of a ransom (usually in bitcoins) to unlock your files. |
| Distribution methods | Infected email attachments (macros), torrent websites, malicious ads. |
| Damage | All files are encrypted and cannot be opened without paying a ransom. Additional password-stealing trojans and malware infections can be installed together with a ransomware infection. |
| Malware Removal (Windows) | To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Malwarebytes. Vlc media player for mac not working. Causes of VLC Player not working VLC Player might not be installed correctly on your system You could be trying to load a corrupt or unsupported file. The VLC Player could have been corrupted as well. VLC allows to play YouTube videos in its interface. Copy any video URL from YouTube. Then go to VLC, press Ctrl+N, paste the URL and play the video. But this is not working for many. Then how to solve this issue? You can set VLC media player to directly play YouTube videos on your Windows. Devices and Mac OS X version VLC media player requires Mac OS X 10.7.5 or later. It runs on any 64bit Intel-based Mac. Previous devices are supported by older releases. While the VLC media player not showing video even the VLC is the latest version, it is time to configure the video output mode settings. Launch you VLC and navigate yourself to the 'preferences' in the submenu from choosing the 'tools' in the menu. Go to the video settings panel by tabbing the 'Video' icon from the left side menu. As of version 3.0, VLC media player gets Chromecast support. Therefore you can cast media files from Windows (10) PC, Mac, and Android to Chromecast. You could then watch your movies on big screen displays. However, many people have come across VLC Chromecast not. |
How to protect yourself from ransomware infections?
To prevent ransomware infections, be very cautious when browsing the Internet. Never open files attached to emails sent from suspicious addresses. These emails should be deleted without reading. Furthermore, download your software from official sources only and, preferably, using a direct download link (third party download/installation tools often include malicious programs). Keep installed programs updated, however, note that criminals proliferate malware via fake updaters. Therefore, updating software via third party tools is very risky. Using a legitimate anti-virus/anti-spyware suite is essential. The main reasons for computer infections are poor knowledge and careless behavior - the key to computer safety is caution.

Text presented within My Decryptor text file:
ALL Y0UR D0CUMENTS, PHOTOS, DATABASES AND OTHER IMP0RTANT FILES HAVE BEEN ENCRYPTED!
Your files are NOT damaged! Your files are modified only. This modification is reversible.
The only 1 way to decrypt your files is to receive the private key and decryption program.
Any attempts to restore your files with the third-party software will be fatal for your files!
To receive the private key and decryption program follow the instructions below:
1. Download 'Tor Browser' from hxxps://www.torproject.org/ and install it.
2. In the 'Tor Browser' open your personal page here:
hxxp://27dh6y1kyr49yjhx8i3.yhicav6vkj427eox.onion/
Note! This page is available via 'Tor Browser' only.
Also you can use temporary addresses on your personal page without using 'Tor Browser':
hxxp://27dh6y1kyr49yjhx8i3.sayhere.party/
hxxp://27dh6y1kyr49yjhx8i3.goflag.webcam/
hxxp://27dh6y1kyr49yjhx8i3.keysmap.trade/
hxxp://27dh6y1kyr49yjhx8i3.segon.racing/
Note! These are temporary addresses! They will be available for a limited amount of time!
Screenshot of My Decryptor Tor website:
Text presented within this website:
MY DECRYPTOR
Your documents, photos, databases and other important files have been encrypted!
WARNING! Any attempts to restore your files with the third-party software will be fatal for your files! WARNING!
To decrypt your files you need to buy the special software - 'My Decryptor'
All transactions should be performed via BITCOIN network.
Within 5 days you can purchase this product at a special price: BTC 0.200 (~ $1141)
After 5 days the price of this product will increase up to: BTC 0.400 (~ $2282)
How to get 'My Decryptor'?
1. Create a Bitcoin Wallet (we recommend Blockchain.info)
2. Buy necessary amount of Bitcoins
3. Send BTC 0.200 to the following Bitcoin address:
18TALbvcZucFZqhui1rowZYiRK5kkwBP1V
4. Control the amount transaction at the 'Payments History' panel below
5. Reload current page after the payment and get a link to download the software
At the moment we have received from you: BTC 0.000 (left to pay BTC 0.200)
Screenshot of files encrypted by My Decryptor ransomware (7 random letters extension):
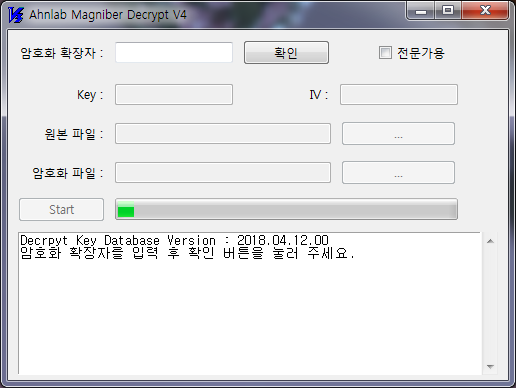
Update 3 April, 2018 - Security researchers from AhnLab have released a free decrypter for this ransomware. Victims can download it HERE.
My Decryptor ransomware removal:
Instant automatic malware removal:Manual threat removal might be a lengthy and complicated process that requires advanced computer skills. Malwarebytes is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
▼ DOWNLOAD MalwarebytesBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Malwarebytes. 14 days free trial available.
Quick menu:
Ahnlab Magniber Decrypt V4.1
- STEP 1. Isolating the infected device.
- STEP 2. Identifying the ransomware infection.
- STEP 3. Searching for ransomware decryption tools.
- STEP 4. Restoring files with data recovery tools.
- STEP 5. Creating data backups.
Isolating the infected device:
Some ransomware-type infections are designed to encrypt files within external storage devices, infect them, and even spread throughout the entire local network. For this reason, it is very important to isolate the infected device (computer) as soon as possible.
Step 1: Disconnect from the internet.
The easiest way to disconnect a computer from the internet is to unplug the Ethernet cable from the motherboard, however, some devices are connected via a wireless network and for some users (especially those who are not particularly tech-savvy), disconnecting cables may seem troublesome. Therefore, you can also disconnect the system manually via Control Panel:
Navigate to the 'Control Panel', click the search bar in the upper-right corner of the screen, enter 'Network and Sharing Center' and select search result:
Click the 'Change adapter settings' option in the upper-left corner of the window:
Right-click on each connection point and select 'Disable'. Once disabled, the system will no longer be connected to the internet. To re-enable the connection points, simply right-click again and select 'Enable'.
Step 2: Unplug all storage devices.
As mentioned above, ransomware might encrypt data and infiltrate all storage devices that are connected to the computer. For this reason, all external storage devices (flash drives, portable hard drives, etc.) should be disconnected immediately, however, we strongly advise you to eject each device before disconnecting to prevent data corruption:
Navigate to 'My Computer', right-click on each connected device and select 'Eject':
How did ransomware infect my computer?
Ransomware-type viruses are proliferated in various ways, however, the most common are: spam emails, third party software download sources, fake software update tools, and trojans. Spam emails often contain malicious attachments (such as JavaScript files, MS Office documents, etc.) that, once opened, download and install malware. Unofficial software distribution sources (peer-to-peer [P2P] networks, free file hosting websites, freeware download websites, etc.) often present malicious executables as legitimate software, thereby tricking users into downloading and running malware . Fake software updaters exploit outdated software bugs/flaws to infect the system. Trojans are the simplest ones - they merely open 'gates' for other malware to infiltrate the system.
| Name | My Decryptor virus |
| Threat Type | Ransomware, Crypto Virus, Files locker |
| Encrypted Files Extension | 7 random characters. |
| Ransom Demanding Message | _HOW_TO_DECRYPT_MY_FILES_[random_characters]_.txt, READ_ME_FOR_DECRYPT_[victim's id].txt, READ_ME.txt, Tor website |
| Ransom Amount | 0.2 Bitcoin |
| Cyber Criminal Contact | Developers provide support via Tor website. |
| Detection Names | Ad-Aware (Gen:Variant.Razy.518505), BitDefender (Gen:Variant.Razy.518505), Emsisoft (Gen:Variant.Razy.518505 (B)), ESET-NOD32 (A Variant Of Win32/GenKryptik.CUTS), Full List Of Detections (VirusTotal) |
| Symptoms | Cannot open files stored on your computer, previously functional files now have a different extension (for example, my.docx.locked). A ransom demand message is displayed on your desktop. Cyber criminals demand payment of a ransom (usually in bitcoins) to unlock your files. |
| Distribution methods | Infected email attachments (macros), torrent websites, malicious ads. |
| Damage | All files are encrypted and cannot be opened without paying a ransom. Additional password-stealing trojans and malware infections can be installed together with a ransomware infection. |
| Malware Removal (Windows) | To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Malwarebytes. Vlc media player for mac not working. Causes of VLC Player not working VLC Player might not be installed correctly on your system You could be trying to load a corrupt or unsupported file. The VLC Player could have been corrupted as well. VLC allows to play YouTube videos in its interface. Copy any video URL from YouTube. Then go to VLC, press Ctrl+N, paste the URL and play the video. But this is not working for many. Then how to solve this issue? You can set VLC media player to directly play YouTube videos on your Windows. Devices and Mac OS X version VLC media player requires Mac OS X 10.7.5 or later. It runs on any 64bit Intel-based Mac. Previous devices are supported by older releases. While the VLC media player not showing video even the VLC is the latest version, it is time to configure the video output mode settings. Launch you VLC and navigate yourself to the 'preferences' in the submenu from choosing the 'tools' in the menu. Go to the video settings panel by tabbing the 'Video' icon from the left side menu. As of version 3.0, VLC media player gets Chromecast support. Therefore you can cast media files from Windows (10) PC, Mac, and Android to Chromecast. You could then watch your movies on big screen displays. However, many people have come across VLC Chromecast not. |
How to protect yourself from ransomware infections?
To prevent ransomware infections, be very cautious when browsing the Internet. Never open files attached to emails sent from suspicious addresses. These emails should be deleted without reading. Furthermore, download your software from official sources only and, preferably, using a direct download link (third party download/installation tools often include malicious programs). Keep installed programs updated, however, note that criminals proliferate malware via fake updaters. Therefore, updating software via third party tools is very risky. Using a legitimate anti-virus/anti-spyware suite is essential. The main reasons for computer infections are poor knowledge and careless behavior - the key to computer safety is caution.
Text presented within My Decryptor text file:
ALL Y0UR D0CUMENTS, PHOTOS, DATABASES AND OTHER IMP0RTANT FILES HAVE BEEN ENCRYPTED!
Your files are NOT damaged! Your files are modified only. This modification is reversible.
The only 1 way to decrypt your files is to receive the private key and decryption program.
Any attempts to restore your files with the third-party software will be fatal for your files!
To receive the private key and decryption program follow the instructions below:
1. Download 'Tor Browser' from hxxps://www.torproject.org/ and install it.
2. In the 'Tor Browser' open your personal page here:
hxxp://27dh6y1kyr49yjhx8i3.yhicav6vkj427eox.onion/
Note! This page is available via 'Tor Browser' only.
Also you can use temporary addresses on your personal page without using 'Tor Browser':
hxxp://27dh6y1kyr49yjhx8i3.sayhere.party/
hxxp://27dh6y1kyr49yjhx8i3.goflag.webcam/
hxxp://27dh6y1kyr49yjhx8i3.keysmap.trade/
hxxp://27dh6y1kyr49yjhx8i3.segon.racing/
Note! These are temporary addresses! They will be available for a limited amount of time!
Screenshot of My Decryptor Tor website:
Text presented within this website:
MY DECRYPTOR
Your documents, photos, databases and other important files have been encrypted!
WARNING! Any attempts to restore your files with the third-party software will be fatal for your files! WARNING!
To decrypt your files you need to buy the special software - 'My Decryptor'
All transactions should be performed via BITCOIN network.
Within 5 days you can purchase this product at a special price: BTC 0.200 (~ $1141)
After 5 days the price of this product will increase up to: BTC 0.400 (~ $2282)
How to get 'My Decryptor'?
1. Create a Bitcoin Wallet (we recommend Blockchain.info)
2. Buy necessary amount of Bitcoins
3. Send BTC 0.200 to the following Bitcoin address:
18TALbvcZucFZqhui1rowZYiRK5kkwBP1V
4. Control the amount transaction at the 'Payments History' panel below
5. Reload current page after the payment and get a link to download the software
At the moment we have received from you: BTC 0.000 (left to pay BTC 0.200)
Screenshot of files encrypted by My Decryptor ransomware (7 random letters extension):
Update 3 April, 2018 - Security researchers from AhnLab have released a free decrypter for this ransomware. Victims can download it HERE.
My Decryptor ransomware removal:
Instant automatic malware removal:Manual threat removal might be a lengthy and complicated process that requires advanced computer skills. Malwarebytes is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
▼ DOWNLOAD MalwarebytesBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Malwarebytes. 14 days free trial available.
Quick menu:
Ahnlab Magniber Decrypt V4.1
- STEP 1. Isolating the infected device.
- STEP 2. Identifying the ransomware infection.
- STEP 3. Searching for ransomware decryption tools.
- STEP 4. Restoring files with data recovery tools.
- STEP 5. Creating data backups.
Isolating the infected device:
Some ransomware-type infections are designed to encrypt files within external storage devices, infect them, and even spread throughout the entire local network. For this reason, it is very important to isolate the infected device (computer) as soon as possible.
Step 1: Disconnect from the internet.
The easiest way to disconnect a computer from the internet is to unplug the Ethernet cable from the motherboard, however, some devices are connected via a wireless network and for some users (especially those who are not particularly tech-savvy), disconnecting cables may seem troublesome. Therefore, you can also disconnect the system manually via Control Panel:
Navigate to the 'Control Panel', click the search bar in the upper-right corner of the screen, enter 'Network and Sharing Center' and select search result:
Click the 'Change adapter settings' option in the upper-left corner of the window:
Right-click on each connection point and select 'Disable'. Once disabled, the system will no longer be connected to the internet. To re-enable the connection points, simply right-click again and select 'Enable'.
Step 2: Unplug all storage devices.
As mentioned above, ransomware might encrypt data and infiltrate all storage devices that are connected to the computer. For this reason, all external storage devices (flash drives, portable hard drives, etc.) should be disconnected immediately, however, we strongly advise you to eject each device before disconnecting to prevent data corruption:
Navigate to 'My Computer', right-click on each connected device and select 'Eject':
Step 3: Log-out of cloud storage accounts.
Some ransomware-type might be able to hijack software that handles data stored within 'the Cloud'. Therefore, the data could be corrupted/encrypted. For this reason, you should log-out of all cloud storage accounts within browsers and other related software. You should also consider temporarily uninstalling the cloud-management software until the infection is completely removed.
Identify the ransomware infection:
To properly handle an infection, one must first identify it. Some ransomware infections use ransom-demand messages as an introduction (see the WALDO ransomware text file below).
This, however, is rare. In most cases, ransomware infections deliver more direct messages simply stating that data is encrypted and that victims must pay some sort of ransom. Note that ransomware-type infections typically generate messages with different file names (for example, '_readme.txt', 'READ-ME.txt', 'DECRYPTION_INSTRUCTIONS.txt', 'DECRYPT_FILES.html', etc.). Therefore, using the name of a ransom message may seem like a good way to identify the infection. The problem is that most of these names are generic and some infections use the same names, even though the delivered messages are different and the infections themselves are unrelated. Therefore, using the message filename alone can be ineffective and even lead to permanent data loss (for example, by attempting to decrypt data using tools designed for different ransomware infections, users are likely to end up permanently damaging files and decryption will no longer be possible even with the correct tool).
Another way to identify a ransomware infection is to check the file extension, which is appended to each encrypted file. Ransomware infections are often named by the extensions they append (see files encrypted by Qewe ransomware below).
This method is only effective, however, when the appended extension is unique - many ransomware infections append a generic extension (for example, '.encrypted', '.enc', '.crypted', '.locked', etc.). In these cases, identifying ransomware by its appended extension becomes impossible.
One of the easiest and quickest ways to identify a ransomware infection is to use the ID Ransomware website. This service supports most existing ransomware infections. Victims simply upload a ransom message and/or one encrypted file (we advise you to upload both if possible).
The ransomware will be identified within seconds and you will be provided with various details, such as the name of the malware family to which the infection belongs, whether it is decryptable, and so on.
Example 1 (Qewe [Stop/Djvu] ransomware):
Example 2 (.iso [Phobos] ransomware):
If your data happens to be encrypted by a ransomware that is not supported by ID Ransomware, you can always try searching the internet by using certain keywords (for example, ransom message title, file extension, provided contact emails, cryptowallet addresses, etc.).
Search for ransomware decryption tools:
Encryption algorithms used by most ransomware-type infections are extremely sophisticated and, if the encryption is performed properly, only the developer is capable of restoring data. This is because decryption requires a specific key, which is generated during the encryption. Restoring data without the key is impossible. In most cases, cyber criminals store keys on a remote server, rather than using the infected machine as a host. Dharma (CrySis), Phobos, and other families of high-end ransomware infections are virtually flawless, and thus restoring data encrypted without the developers' involvement is simply impossible. Despite this, there are dozens of ransomware-type infections that are poorly developed and contain a number of flaws (for example, the use of identical encryption/decryption keys for each victim, keys stored locally, etc.). Therefore, always check for available decryption tools for any ransomware that infiltrates your computer.
Finding the correct decryption tool on the internet can be very frustrating. For this reason, we recommend that you use the No More Ransom Project and this is where identifying the ransomware infection is useful. The No More Ransom Project website contains a 'Decryption Tools' section with a search bar. Enter the name of the identified ransomware, and all available decryptors (if there are any) will be listed.
Restore files with data recovery tools:
Depending on the situation (quality of ransomware infection, type of encryption algorithm used, etc.), restoring data with certain third-party tools might be possible. Therefore, we advise you to use EaseUS Data Recovery Wizard Pro. This tool supports over a thousand data types (graphics, video, audio, documents, etc.) and it is very intuitive (little knowledge is necessary to recover data).
By downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. Trial version of EaseUS Data Recovery Wizard Pro is capable of scanning drives and listing recoverable files - to restore them, you must purchase a license.
Step 1: Perform a scan.
Hover your mouse over the partition you wish to scan and select 'Scan'. You can also select a specific folder, or click shortcut icons to scan the Desktop or Recycle Bin:
Wait for EaseUS Data Recovery Wizard Pro to complete the scan. The scanning duration depends on the volume of files (both in quantity and size) that you are scanning (for example, several hundreds gigabytes could take over an hour to scan). Therefore, be patient during the scanning process. We also advise against modifying or deleting existing files, since this might interfere with the scan. If you add additional data (for example, downloading files/content) while scanning, this will prolong the process:
Step 2: Recover data.
Once the process is complete, select the folders/files you wish to restore and simply click 'Recover'. Note that some free space on your storage drive is necessary to restore data. Note also that the trial version of EaseUS Data Recovery Wizard Pro is only capable of scanning drives and listing recoverable files - to restore them, you must purchase a license:
Step 3: Save the scan session (optional).
We recommend that you save the scanning session once you have completed recovery, in case you decide to recover additional files later. Simply click the 'Save Scan Session' icon in the upper-right corner of the screen and choose the location for the file to be saved. This will save a lot of time, since you will not need to re-scan the storage drive the next time you wish to restore something. Bear in mind, however, that data removed after the scanning session has finished will not be listed:
Create data backups:
Proper file management and creating backups is essential for data security. Therefore, always be very careful and think ahead.
Partition management: We recommend that you store your data in multiple partitions and avoid storing important files within the partition that contains the entire operating system. If you fall into a situation whereby you cannot boot the system and are forced to format the disk on which the operating system is installed (in most cases, this is where malware infections hide), you will lose all data stored within that drive. This is the advantage of having multiple partitions: if you have the entire storage device assigned to a single partition, you will be forced to delete everything, however, creating multiple partitions and allocating the data properly allows you to prevent such problems. You can easily format a single partition without affecting the others - therefore, one will be cleaned and the others will remain untouched, and your data will be saved. Managing partitions is quite simple and you can find all necessary information on Microsoft's documentation web page.
Data backups: The most reliable backup method is to use an external storage device and keep it unplugged. Copy your data to an external hard drive, flash (thumb) drive, SSD, HDD, or any other storage device, unplug it and store it in a dry place away from sun and extreme temperatures. This method is, however, quite inefficient, since data backups and updates need to be made regularly. You can also use a cloud service or remote server. Here, an internet connection is required and there is always the chance of a security breach. Therefore, you should consider using an application to create data backups locally.
By downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for EaseUS Todo Backup. 30 days free trial available.
Ahnlab Magniber Decrypt V4
We recommend using the EaseUS Todo Backup application. The 'Home' edition of EaseUS Todo Backup is usually more than adequate for regular users, however, the 'Business' edition is more suitable for companies and large computer networks. The EaseUS Todo Backup application provides extensive data protection features. You can easily create backups, and encrypt and compress them for enhanced protection and storage saving purposes. It also allows you to set backup schedules, create bootable devices, and restore the system if a crash occurs. You can easily choose where to store the created backup: locally; uploaded to an external drive; FTP; cloud storage, or elsewhere. In summary, EaseUS Todo Backup is an all-in-one tool, which provides all features required to properly backup your data.
Creating a data backup:
The backup process is virtually identical regardless of the item (file, partition, entire system) you wish to backup. Taking the File Backup feature as an example:
Step 1: Choose which item to backup.
Click on the 'Menu' icon in the upper-left corner of the screen to reveal the menu and select 'File Backup':
Select the files you want to backup. You can also enter a name and description of the backup that will be created:
Step 2: Change the default settings.
The EaseUS Todo Backup application provides a variety of additional options that can be added/modified while creating the backup. For example, you can encrypt data (add a password), select the compression rate (how much the backup should be compressed), performance (how many system resources should be allocated), add an email notification (you receive an email once the process is complete) and so on.
To open the options window, click the 'Backup options' button in the lower-left corner of the screen:
Select the settings you want to change and click 'Save'. You can also reset your changes by clicking 'Reset to initial settings':
Step 3: Select the backup destination.
As mentioned above, EaseUS Todo Backup allows you to choose where backups are saved - locally or externally.
Click the 'Browse..' button and select the location you want the backup to be saved:
Step 4: Safety measures and process completion.
Depending on the location you have chosen, there are a number of measures you should or should not take. If you are uploading to an internet-connected location (for example, Cloud storage, FTP, etc.), be sure to maintain your internet connection, otherwise you will have to start again. The same applies to external storage devices - do not unplug them until the process is complete.
The progress bar displays estimated time remaining until completion. Large backups (hundreds of gigabytes) can take hours to create (depending on storage device speed, internet connection, etc.). Therefore, the application also allows you to optionally choose what the system should do (shut down, sleep or hibernate) once the process has finished:
The best way to avoid damage from ransomware infections is to maintain regular up-to-date backups.
